The £200 device that could steal your bank PIN.
The increasing availability of cheap thermal imaging equipment -once the sole preserve of only the best equipped attacker- is creating an ever increasing risk to push button security devices. Using a readily available IPhone accessory costing less than £200, Sec-Tec tested a wide range of push button security devices, including ATMS, locks and safes, and found that certain devices could leak the digits pressed by a legitimate user for over a minute after use:

PIN 1567 entered into an Internet banking authenticator
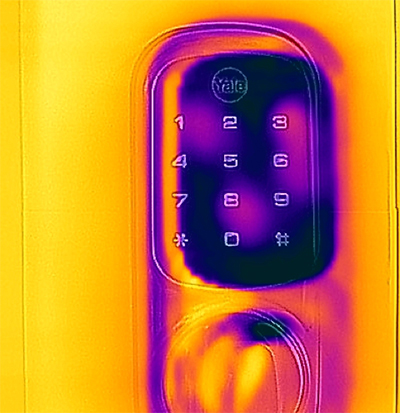
PIN 1836 entered into an electronic door lock
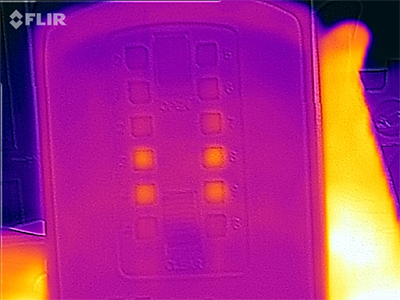
Digits pressed on a wall mounted key safe were clearly visible for some time after use
While identifying the keys in use is trivial, identifying the order in which they were pressed is considerably more difficult. However, Sec-Tec have identified two undisclosed methods that assist considerably in the identification of key ordering, and many of the devices utilise no lockout, so testing all combinations of a four digit code once the digits are known is trivial.
Sec-Tec make the following recommendations to limit the risk of attack:
1. The use of devices with metallic keys, as opposed to plastic or rubber keys, renders this attack unfeasible.
2. Palming the keypad after use, even for only a few seconds, prevented the attack in the majority of cases.
Sec-Tec have combined this attack vector together with existing RFID cloning equipment to successfully compromise two factor door locks on a physical penetration test assignment.
Great to see that after posting this item people are carrying on the conversation:-
http://observer.com/2015/08/this-cheap-iphone-attachment-can-help-crimin...
http://www.theregister.co.uk/2015/08/21/thermal_imaging_security_risk/
http://eandt.theiet.org/news/2015/aug/thermal-pin.cfm
http://www.itnews.com.au/News/408178,cheap-thermal-imagers-can-steal-use...
http://www.ibtimes.co.uk/iphone-android-accessory-can-help-thieves-steal...
http://jonathanturley.org/2015/08/22/thermal-imaging-cameras-might-be-us...
http://www.hackbusters.com/news/stories/369230-pins-easily-pinched-with-...
